The Agentic MDR Pipeline: Detection Engineering at Scale

Sr. Technical Content Strategist

A CVE surfaces in the morning. By the time you are talking to that customer, you can tell them: we saw it, we checked your environment, you were not affected, and we deployed a rule that will catch it if it ever shows up.
For MSSPs and MDR providers, detection engineering is among the most valuable services you can offer. It is also among the most expensive to deliver consistently and at scale.
When it works well, it looks like this:
Your team monitors the threat landscape daily
They map new intelligence to each customer's environment
They write detection rules tailored to each customer's specific exposure
They validate the rules against real telemetry
You deliver a continuous stream of coverage improvements
Every customer’s security posture keeps pace with current threats, and you can prove the value of your service with concrete outputs.
When it breaks down, it looks like this:
Detection rules go stale
Threat intel sits in a queue nobody has time to process
Coverage gaps accumulate silently
Engineers are spread too thin to cover every customer adequately
LimaCharlie's MDR hunting pipeline automates this cycle while keeping it under your control. Agentic operators run daily, across all your customer tenants, without requiring a dedicated detection engineering team to function. Our pipeline is open source, fully auditable, and modifiable.
The business case is straightforward: you deliver a mature, continuous detection engineering program to every customer on your roster, at a fraction of the cost of doing so manually. Your engineers spend their time on work that requires human judgment, not on the repeatable mechanics of processing threat intel and drafting rules.
Why Traditional Detection Engineering Is Hard to Scale
Detection engineering done well is an ongoing operational discipline, and the workload compounds as your customer base grows.
The core challenge is context. A rule that catches malicious behavior in one organization generates noise in another. Writing accurate, specific rules that avoid false positives requires knowing each customer's environment: what operating systems they run, what SaaS platforms they use, what their normal traffic patterns look like. That profiling work is manual, time-consuming, and needs regular refreshing as environments change.
Layered on top of that is managing the sheer volume of threat intelligence. Botnet IOC feeds, breach reports, CVE disclosures, attacker TTPs, open-source rule repositories: the amount of relevant intelligence that arrives daily exceeds what most teams can process. Filtering it to what matters for each customer, then translating it into actionable detections, requires both security expertise and considerable time.
Then there is validation. A detection rule untested against real telemetry is a liability, not an asset. Unit testing, retroactive hunting against historical data, and tuning to eliminate false positives are necessary steps before a rule is ready to deploy. In practice, those steps get skipped or rushed when engineers are under pressure.
A mature detection engineering program requires dedicated headcount: people who follow the threat landscape, understand customer environments, write and validate rules, and track coverage over time. For MSSPs managing dozens or hundreds of tenants, that headcount scales with the customer count. The economics work against you.
For most MDR and MSSP operations, the result is a detection program that is reactive rather than proactive. Coverage is inconsistent across customers and perpetually behind the current threat landscape.
How LimaCharlie's MDR Hunting Pipeline Works
LimaCharlie's MDR hunting pipeline is a team of AI agents that executes the full detection engineering cycle automatically, every day, across all your customer tenants.
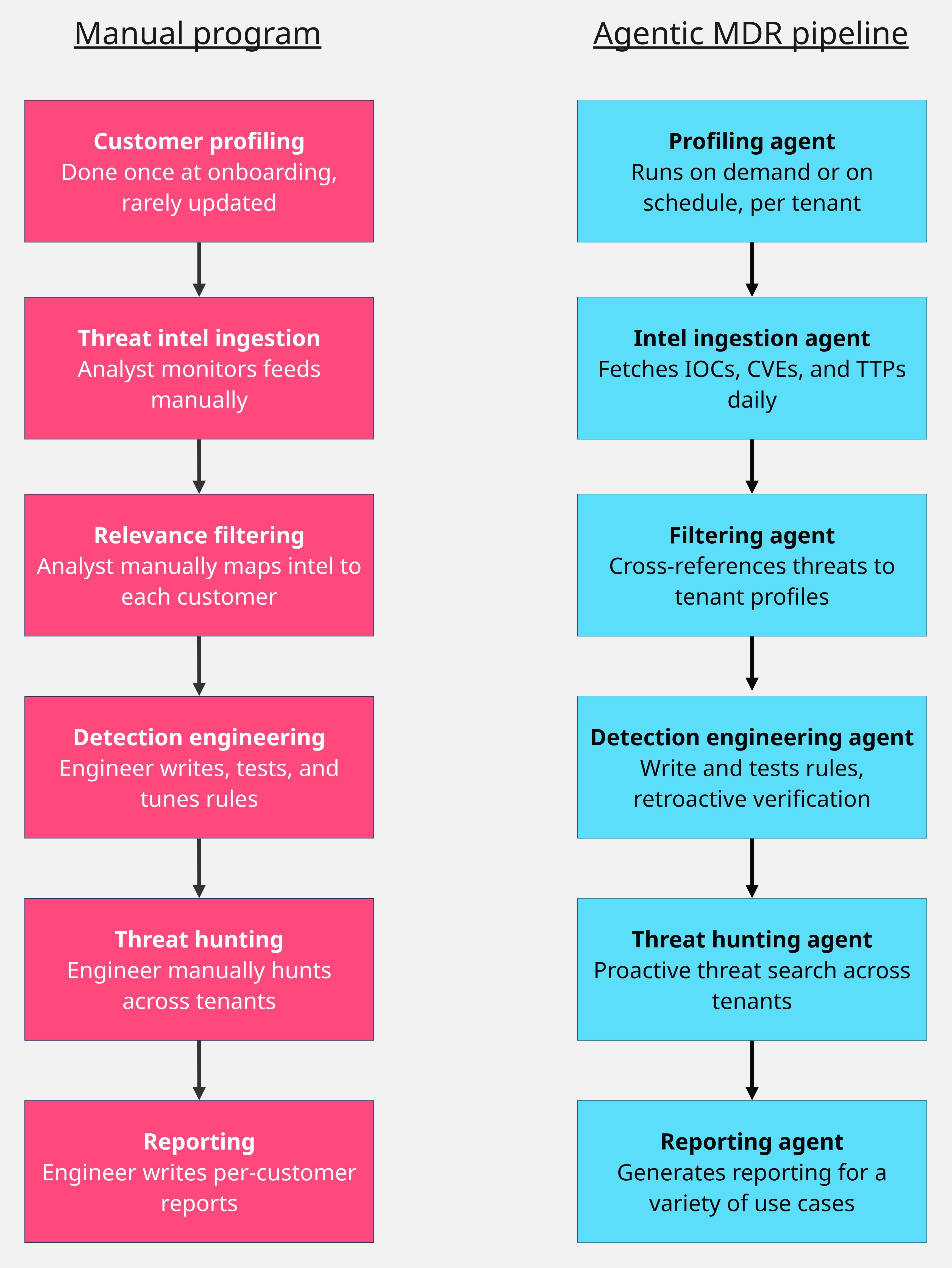
Each stage of the pipeline maps directly to a stage in a manually operated detection engineering program. The difference is that the pipeline runs continuously, at scale, without a team of engineers to operate it. This is agentic AI security applied to one of the hardest operational problems in managed security.
Here is what the pipeline does, and what it replaces.
Customer profiling: A mature detection engineering program starts with knowing your customers: what operating systems, SaaS platforms, and key infrastructure they run. Manually, this profiling work is done once during onboarding and updated sporadically. In the pipeline, a profiling agent runs weekly and on demand, refreshing an accurate picture of each tenant's environment. When threat intelligence arrives, the pipeline already knows which customers are affected.
Threat intelligence ingestion: The pipeline fetches threat intelligence daily from open-source feeds, covering the full spectrum of relevant signals: botnet IOCs, breach reports, CVE disclosures, and attacker TTPs. Manually, this requires an analyst to monitor multiple sources, filter the noise, and determine what is actionable. The pipeline handles ingestion and initial filtering automatically, with no feed management required.
Relevance filtering: Raw threat intelligence is not actionable until mapped to your customers' environments. The pipeline cross-references incoming intelligence against each customer's profile and filters out irrelevant signals. A CVE affecting a platform none of your customers run gets deprioritized. An IOC targeting Windows environments gets escalated for customers running Windows. The output is a focused, customer-specific picture of what needs attention that day.
Detection engineering: A detection engineer reviews filtered intelligence, writes rules targeting the relevant behaviors, and prepares them for deployment. In the pipeline, a detection engineering agent does this work automatically. It writes rules targeting the IOCs and attacker behaviors identified in the filtered intelligence. It writes unit tests for each rule and runs retroactive hunting against historical telemetry for each tenant. The agent then iterates on the rules, tuning false positive suppression until they are ready for review. For agentic security MSSP operations, this is where the pipeline delivers its most significant leverage.
Threat hunting: Once new detections are in place, the pipeline does not wait for the next alert. A threat hunting agent searches proactively across all tenants, looking for evidence that the threats identified in the daily intelligence are already present in any customer environment. If it finds something, it opens a case. If it finds nothing, it documents that too, giving you a record that the environment was clear. This capability functions as continuous AI SOC automation running in the background of your operation.
Reporting: The pipeline produces two levels of output. A per-customer report summarizes what was found, what rules were written, whether the customer was affected, and what they should consider patching or updating. An aggregate report gives the MDR team a full picture of the day's activity across all tenants. Both reports are ready to share with customers directly or use as the basis for a tailored communication.
In practice, this delivers daily proof of value for every customer on your roster. A CVE surfaces in the morning. By the time you are talking to that customer, you can tell them: we saw it, we checked your environment, you were not affected, and we deployed a rule that will catch it if it ever shows up.
Most MDRs cannot make that claim. With the MDR pipeline running, it becomes routine.
For agentic security MSSP operations, the pipeline also changes the economics of adding new customers. Each new tenant gets the same detection engineering coverage from day one, without requiring incremental engineering hours for setup and maintenance. The pipeline scales with your customer base. Your team does not have to.
Detection Engineering Across Every Tenant, Every Day
Detection engineering has always been a differentiator for MDR and MSSP providers. Delivering it consistently, across every customer and at scale, has required more resources than most teams have.
LimaCharlie's MDR hunting pipeline removes that constraint. It does not replace your engineers. It gives them a force multiplier: a system that handles the repeatable mechanics of the detection engineering cycle so your team can focus on the work that requires human judgment. Teams already using LimaCharlie for AI for incident response and agentic AI security will find the pipeline fits naturally into their existing workflows.
Our MDR pipeline has no black boxes. You can inspect and change any part of it because every agent's prompt and parameters are visible. To add a proprietary threat intelligence feed, adjust the profiling logic for a specific customer, or change how reports are formatted, simply edit the prompt. You are not locked into a vendor's interpretation of what good detection engineering looks like.
Visit https://app.limacharlie.io/signup to explore the platform or speak with our team about what the MDR hunting pipeline looks like in your environment.
440 N Barranca Ave #5258
Covina, CA 91723
5307 Victoria Drive #566
Vancouver, BC V5P 3V6
Stay up-to-date on all things LimaCharlie with our monthly newsletter.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.